4IR More of a Security Opportunity Than a Threat
The emerging technologies linked to the fourth industrial revolution (4IR) offer more security opportunities than security risks, but many companies still don't perceive it that way.
This is according to new research study entitled "The State of Enterprise Security in South Africa 2019," conducted by technology market research company World Wide Worx and commissioned by Trend Micro and VMware. The study surveyed IT decision makers at 220 enterprises across all industries in South Africa on the centrality of cybersecurity in business strategy, the vulnerability of businesses, and security compliance.
"We looked at the emerging technologies that are regarded as underpinning the fourth industrial revolution from a point of view of vulnerability, but also opportunity. I think this is the first time that research has been done in this country in terms of how vulnerable 4IR technologies leave the enterprise," Arthur Goldstuck, MD of World Wide Worx, said at a press event in Johannesburg on Wednesday where the findings were unveiled.
Goldstuck said there is a perception that 4IR tech is a big threat when it comes to cybersecurity for enterprises, but the research found that the security advantages outweigh the risks.
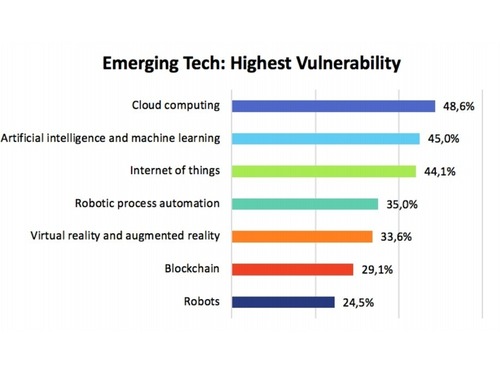
When those surveyed were asked about the highest perceived vulnerabilities from emerging tech, cloud computing came out on top, with just under half of all organizations (48.6%) believing it leaves them highly vulnerable to cyber attacks. Meanwhile, 45% thought artificial intelligence (AI) and machine learning (ML) opened them up to threats; and 44.1% of those surveyed thought the Internet of Things (IoT) left them highly vulnerable.
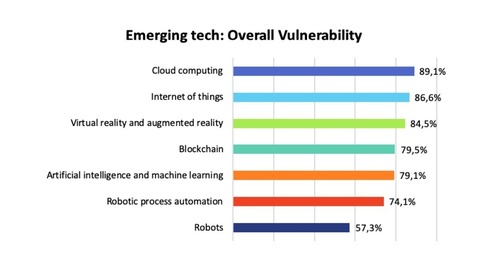
When you look at the overall vulnerability of these technologies (ranked as somewhat and highly vulnerable), cloud computing was still in the lead, but at a far higher percentage of 89.1%. IoT jumped up higher on the list, with 86.6% of those surveyed seeing it as a general risk, followed by VR and AR at 84.5%.
Interestingly, blockchain also comes up higher in the list, at 79.5%, which is ironic, as Goldstuck explained: "Blockchain is meant to increase trust and authentication in organizations, transactions and operations, but it is seen as being vulnerable as well".
Over three quarters of organizations view most emerging technologies as leaving them vulnerable.
"Robots interestingly come in far lower again at 57.3%. So, the consumer and the labor unions feel very threatened by robots but in terms of cybersecurity they are the least dangerous of all. It almost takes away that fictional fear of robots when it comes to the security environment. Why? Because robots typically only output what you input, and they are not really a point of entry into the organization. They are really just an ambassador or a symbol of the organization's involvement in technology," Goldstuck said.
"So yes, the fourth industrial revolution leaves organizations highly vulnerable, but the flipside of it is [that] the extent to which it can be used to protect the organizations in fact outweighs the extent to which it can leave them vulnerable," he added.
Opportunity emerges
In fact, AI and ML were seen as the most powerful forms of protection from cyber attacks, with 60.9% of respondents believing that their organizations will benefit highly from the levels of protection that AI and ML can bring. Cloud computing is a little behind, at 53.2%, followed by 50.5% for VR and AR.
"It increases quite significantly when you look at the general benefit, with more than three quarters of organizations believing that most of these emerging technologies will in fact enhance their ability to protect the organization from cyber attacks," Goldstuck adds.
In general, cloud computing comes out with the highest overall benefit to security (86.8%), followed by VR and AR (85.9%) and then blockchain (80.9%).
Cloud computing makes organizations more vulnerable in some ways and stronger in others, while technologies like AI and ML can have a major benefit when it comes to security. Goldstuck said you can see the positives in what vendors like Trend Micro and VMware are doing, because they are implementing AI and ML solutions to help protect businesses.
"It's one area where vendors are ahead in the arms race against cybercriminals, because traditionally cybercriminals are perceived as being ahead in the race, but with AI it needs such massive resources that at the moment the vendors are winning that race," Goldstuck added.
The biggest shortcoming in cybersecurity preparedness was highlighted as outdated software and infrastructure, with 77% of IT decision-makers reporting that it makes their organizations highly vulnerable. Goldstuck said that the opportunity presented by 4IR technologies could help alleviate this, but he believed that in general enterprises are not quite ready for this.
"This is where 4IR could take organizations eventually. At the moment we think we are ready, but clearly we are not."
Imminent attack
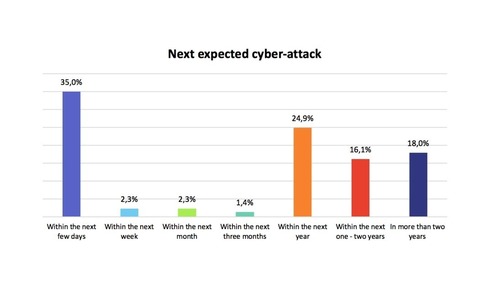
What the research also found was that, with cybercrime on the rise, more than a third of South Africa IT decision-makers are on high alert and 35% are actually expecting cyber attacks within days. On the other end of the scale, 18% of those surveyed think they are safe from attack in the next two years.
When it comes to detection, 56.7% of businesses say they will detect evidence of a malicious breach within a few minutes. However, 33.6% of businesses won't know they've been compromised for a few hours and the rest for even longer after a security breach.
Goldstuck said such businesses may be in for a big shock because ransomware and other file-destroying malware may corrupt almost every file on a user's computer within a few hours, which means any delayed response will ultimately be too late.
Surprisingly, IT decision-makers are willing to accept responsibility. Half of the respondents said they would blame their own departments in the event of a breach.
But the survey did reveal a disconnect between who would be aware of data breaches and who should be aware of data breaches. Over a third of IT decision-makers reported that the IT department would be the most aware of the actions to take after a data breach, while over half of IT decision-makers reported that their chief information officers should be the most aware of how to navigate the organization after a data breach.
"We were astonished when we found that CIOs don't lead the organization's response to a data breach," said Lorna Hardie, VMware regional director for Sub-Saharan Africa. "This finding shows that organizations still have a long way to go in terms of connecting a CIO's strategy to that of the IT department.
Goldstuck said the results lead us to imagine that IT departments must feel under siege, yet they are supremely confident in their ability to protect companies.
"Any question relating to their capacity and capability is met with resounding confidence, suggesting that they are either over-confident, or supremely arrogant. At best, we would say that they don't want to be perceived as falling down on the job and can cope regardless of the obstacles in their way and the threat out there."
He said that although 99% said they were confident about protecting the company, the picture disintegrates when asked if they have the skills to do so, with 45% agreeing that they don't have the skills to protect the company.
* All graphs courtesy of World Wide Worx.
Paula Gilbert, Editor, Connecting Africa